by Roderick W. Smith, rodsmith@rodsbooks.com
Originally written: 11/13/2012; last Web page update: 11/13/2012, referencing rEFInd 0.5.0
I'm a technical writer and consultant specializing in Linux technologies. This Web page is provided free of charge and with no annoying outside ads; however, I did take time to prepare it, and Web hosting does cost money. If you find this Web page useful, please consider making a small donation to help keep this site up and running. Thanks!
| Donate $1.00 | Donate $2.50 | Donate $5.00 | Donate $10.00 | Donate another value |
This page is part of the documentation for the rEFInd boot manager. If a Web search has brought you here, you may want to start at the main page.
If you're using a computer that supports Secure Boot, you may run into extra complications. This feature is intended to make it difficult for malware to insert itself early into the computer's boot process. Unfortunately, it also complicates multi-boot configurations such as those that rEFInd is intended to manage. This page describes some secure boot basics and two specific aspects of rEFInd and its interactions with Secure Boot: installation issues and key management.
Through 2012, it became obvious that Secure Boot would be a feature that was controlled, to a large extent, by Microsoft. This is because Microsoft requires that non-server computers that display Windows 8 logos ship with Secure Boot enabled. As a practical matter, this also means that such computers ship with Microsoft's keys in their firmware. In the absence of an industry-standard body to manage the signing of Secure Boot keys, this means that Microsoft's key is the only one that's more-or-less guaranteed to be installed on the computer, thus blocking the ability to boot any OS that lacks a boot path through Microsoft's signing key.
Fortunately, Microsoft will sign third-party binaries with their key. A payment of $99 to Verisign enables a software distributor to sign as many binaries as desired. Red Hat (Fedora), Novell (SUSE), and Canonical (Ubuntu) have all announced plans to take advantage of this system. Unfortunately, using a third-party signing service is an awkward solution for open source software. In fact, for this very reason Red Hat has developed a program that it calls shim that essentially shifts the Secure Boot "train" from Microsoft's proprietary "track" to one that's more convenient for open source authors. Shim is signed by Microsoft and redirects the boot process to another boot loader that can be signed with keys that the distribution maintains and that are built into shim. Fedora 18 is expected to use this system. SUSE has announced that it will use the same system, as does Ubuntu with version 12.10 and later. SUSE has contributed to the shim approach by supporting a set of keys that users can maintain themselves. These keys are known as Machine Owner Keys (MOKs), and managing them is described later, in Managing MOKs. To reiterate, then, there are potentially three ways to sign a binary that will get it launched on a system that uses shim:
All three key types are the same in form—shim's built-in keys and MOKs are both generated using the same tools used to generate Secure Boot keys. Unfortunately, the tools used to generate these keys are still rather crude and are rarely installed on Linux systems, which is one of the reasons that rEFInd's installation script doesn't yet support setting up a Secure Boot configuration. Although it's theoretically possible to use rEFInd without signing your own binaries, this is not yet practical, because distributions don't yet provide their own signed binaries or the public MOK files you must have to enroll their keys. With any luck this will change in 2013. At the very least, many distributions will begin supporting Secure Boot in the near future, and with any luck they'll include their public MOKs for use with other distributions' versions of shim.
Because shim and MOK are being supported by several of the major players in the Linux world, I've decided to do the same with rEFInd. Beginning with version 0.5.0, rEFInd can communicate with the shim system to authenticate boot loaders. If a boot loader has been signed by a valid UEFI Secure Boot key, a valid shim key, or a valid MOK key, rEFInd will launch it. rEFInd will also launch unsigned boot loaders or those with invalid signatures if Secure Boot is disabled in or unsupported by the firmware. (If that's your situation, you needn't bother reading this page.)
A working Secure Boot installation of rEFInd involves at least three programs, and probably four or more, each of which must be installed in a specific way:
Because of variables such as which version of shim you're using and whether you intend to rely exclusively on shim keys or make use of MOKs, I can't provide an absolutely complete procedure for installing rEFInd to work with Secure Boot. Broadly speaking, though, the procedure should be something like this:
At this point the computer may boot into its default OS, reboot, or perhaps even hang. When you reboot it, though, rEFInd should start up in Secure Boot mode. It should now be able to launch any boot loader signed with a key recognized by the firmware or by shim (including any MOKs you've enrolled). If you want to manage keys in the future, rEFInd displays a new icon in the second (tools) row you can use to launch MokManager. (This icon appears by default, but if you edit showtools in refind.conf, you must be sure to include mok_tool as an option in order to gain access to it.)
Several variants on this procedure are possible. For instance, you can generate your own MOK, sign rEFInd with it, and enroll that MOK rather than the refind.der MOK. If you're using Ubuntu 12.10, you can't use its version of shim, but you can replace it with Garrett's shim. The problem is that Ubuntu's GRUB and kernel will then be signed by an unknown key. Unfortunately, I haven't found a suitable public key file on Ubuntu's distribution medium, so you may need to sign GRUB and/or your kernels with your own MOK. In principle, you should be able to use shim 0.2 or later from future distributions that include it; but you must be sure that whatever you use supports MokManager.
The idea behind MOKs is that you should be able to control the signing of your boot loader binaries. Broadly speaking, you can add recognized signing keys in either of two ways:
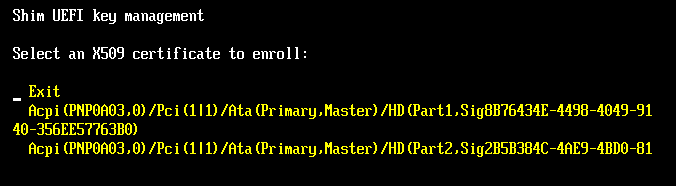
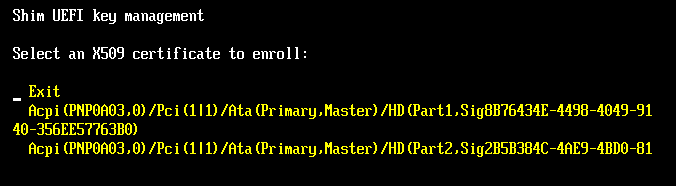
As I write, the methods for adding MOKs from the OS remain unclear to me, so I don't address them here. MOK management using MokManager, though, is fairly straightforward, as described earlier, near the end of Installation Issues. The main caveat is that the MokManager user interface is extremely crude. A directory that contains too many entries tends to produce drawing errors that can interfere with selecting the correct file. Thus, I recommend keeping your ESP's root directory uncluttered and place any .der files you need in an equally uncluttered directory off of the root directory.
The biggest challenge to managing MOKs comes if you need to sign binaries using your own keys. This task requires using cryptographic software based on OpenSSL. The tools involved are crude and poorly documented. I describe a procedure for creating keys and signing binaries here, so check that page if you need detailed instructions.
copyright © 2012 by Roderick W. Smith
This document is licensed under the terms of the GNU Free Documentation License (FDL), version 1.3.
If you have problems with or comments about this Web page, please e-mail me at rodsmith@rodsbooks.com. Thanks.
Return to my main Web page.